F-Response and the ASI Forensic Scanner
Oct 18, 2012
Just the other day I noticed a tweet from Harlan Carvey regarding his newly released "ASI Forensic Scanner". From his blog:
"The forensic scanner is a targeted tool with a specific purpose, and not a general analysis framework. Instead, much like other scanners (Nessus, ISS's Internet Scanner, etc.), the forensic scanner is intended to fill a gap; using frameworks and applications...analysts will find artifacts and indicators of compromise, and then document them as plugins as a means of automation. Then whenever the scanner is run against an acquired image, checks for those artifacts, as well as processing and even inclusion of references, are run automatically. This is intended to quickly allow the analyst to analyze, by running checks that have already been discovered. Learn it once, document it, run it every time."
Harlan recently posted the Forensic Scanner on Google Code, so the first logical thing for us to do was test it with F-Response. We fired up a virtual machine in our test environment, deployed F-Response and connected to PhysicalDrive0. In seconds we had a "G:\" volume we could run the Forensic Scanner against to get an overview of Incident Response based data on the remote machine.
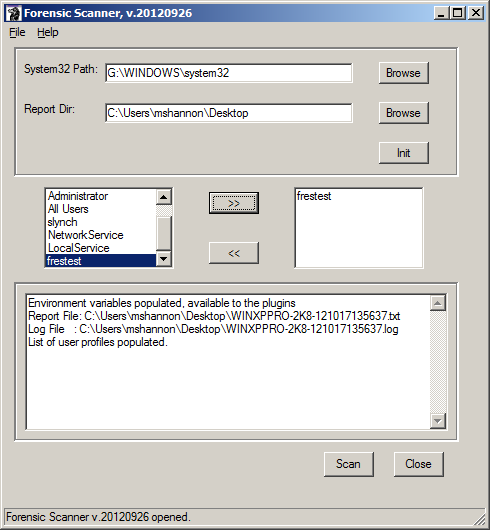
The process was very straight forward, provided you follow the instructions and run the Forensic Scanner as Administrator, after that is was very easy to locate the system32 folder and select one or more profiles to review.
The reports produced were considerably information dense. There's plenty of data being extracted and exposed by the Forensic Scanner, even after a cursory review I'm convinced it will save steps and effort during an IR project.
Interested in giving it a try? You'll find the Forensic Scanner on Google Code at http://code.google.com/p/forensicscanner/ . Also an F-Response customer? The Forensic Scanner will work fine with F-Response targets from Field Kit to Enterprise, and everything in between!
Thanks for sharing Harlan!
Warmest Regards,
M. Shannon, Principal
F-Response
October 18, 2012