An Interview with Jason Hale of USB Detective
May 06, 2014
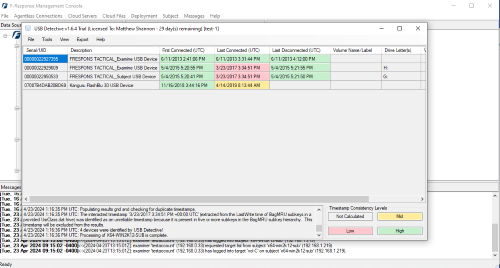
A few days ago we profiled USB Detective, a fascinating desktop application for USB device artifact forensics.
Since that time, we reached to Jason Hale of USB Detective to get a little more information on his vision for computer forensics and USB Detective itself.
You'll find our interview below:
F-Response: What is your background in Computer Forensics? How did you get into the field?
Jason: "I got into the field in 2008 when I started working for a small digital forensics consulting company. I started out learning digital forensic acquisition processes as well as data recovery techniques. After a bit, I transitioned into conducting forensic analysis and found that I really loved the work. I enjoy the challenge of finding “the needle in the stack of needles” and deciphering the state of a system to determine what activity took place previously on the system. Earlier in my career, I spent countless nights staying up far too late reading books like File System Forensic Analysis, Windows Internals, Windows Registry Forensics, and more. I realized that the better I understood the underlying systems where the forensic artifacts are stored, the better I was able to examine them, to understand the limitations of my findings, and explain them when needed."
F-Response: How did you come up with USB Detective? What was your inspiration?
Jason: "The idea for USB Detective was born when I was walking a colleague through the methodology of USB device forensics. I was explaining the nuances that come with different types of USB drives, how different Windows versions can impact the location of artifacts, and how there are so many data points to cross-correlate and check against one another when conducting USB device forensics. In explaining that methodology, I realized that there was an opportunity there to develop something that could not only make my life easier when conducting USB device forensics but help others to perform the same type of analysis with a much smaller learning curve."
F-Response: Do you have a favorite customer win story with USB Detective?
Jason: "That’s a tough one! I love hearing about when customers find something they weren’t expecting with USB Detective, such as when a previous connection time of a device is uncovered that paints an entirely different picture of when the device was used and calls into question statements that were made during the course of litigation. I also love hearing about how customers are leveraging the various USB Detective reports – especially the timeline – to uncover patterns in the evidence and better understand the usage of a device."
F-Response: Where do you see USB Detective going in the future?
Jason: "I see USB Detective continuing to support the new versions of Windows as new artifacts are released or changed down the line. We really value customer feedback and look forward to continuing to improve USB Detective by incorporating commonly requested features. We are also working on a building a training curriculum for those that want a deep dive into USB device forensics and how to get the most out of USB Detective."
Thanks for taking the time to answer our questions, Jason, and for letting us show off USB Detective to our readers and users.
You can find more about USB Detective on their website, usbdetective.com.
And more about using USB Detective over F-Response in the original blog post.
Warmest Regards,
M Shannon
F-Response